Data logger security
Data logger security concerns include:
- Collection of sensitive data
- Operation of critical systems
- Networks that are accessible to many individuals
Secure by default
Data loggers with ![]() UID Unique identifiers are secure by default. This means a
UID Unique identifiers are secure by default. This means a ![]() PakBus Encryption Key A PakBus Encryption Key is a security feature used with Campbell Scientific data loggers that communicate via the PakBus protocol. It helps protect data and restrict unauthorized access to the data logger. is enabled by default. The default PakBus Encryption Key is the UID.
PakBus Encryption Key A PakBus Encryption Key is a security feature used with Campbell Scientific data loggers that communicate via the PakBus protocol. It helps protect data and restrict unauthorized access to the data logger. is enabled by default. The default PakBus Encryption Key is the UID.
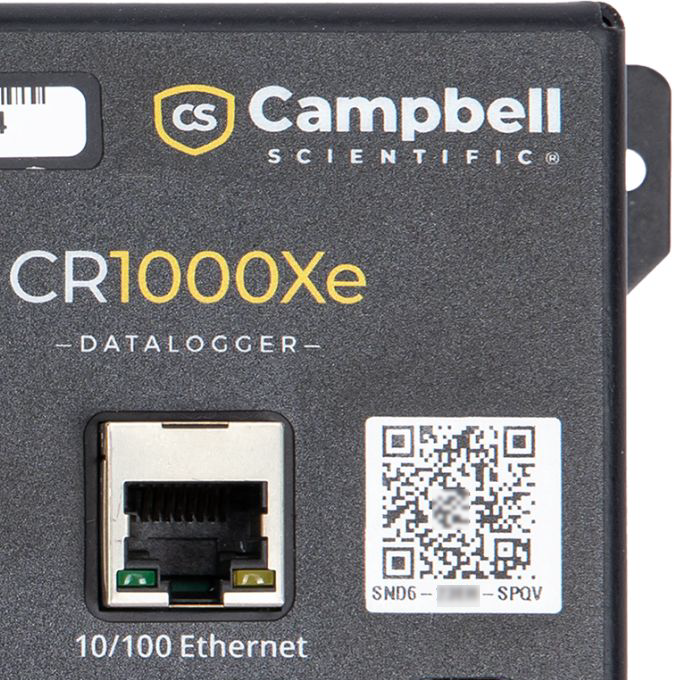
The ![]() UID Unique identifier can be found on a QR-code on the front of the data logger.
UID Unique identifier can be found on a QR-code on the front of the data logger.
CR1000X/CR1000Xe data loggers shipped before the release of UIDs and running operating system
Direct USB connections do not require that you enter the PakBus Encryption Key, unless USB Not Trusted is enabled in the data logger.
Other Secure by default features
Anonymous HTTP access is disabled by default. HTTP will be accessible with admin as the username and UID as the admin password. See Web services for more information.
FTP is disabled by default. However, when enabled, the UID will be the default FTP password. See Network services for more information.
Wi-Fi, when configured as an Access Point (“Create a Network”), will use the UID as the default password.
When a data logger has a UID and is reset to factory defaults, the UID will be used as the default password.
Passwords may be changed from the default UID. However, when the data logger is reset to factory defaults or a new OS is sent, the default password will revert to the UID.
Check the CR1000X/CR1000Xe operating system version as outlined in Updating the operating system, and update as needed.